Addressing dark web crime requires enhanced cybersecurity infrastructure, better enforcement of laws: former FIA DG

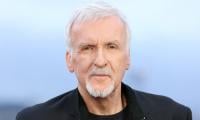
The dark web, a concealed part of the internet accessible only through specialized software like Tor, provides anonymity for its users. While this anonymity protects freedom of expression in oppressive regimes, it also fosters criminal enterprises such as drug trafficking, human trafficking, arms dealing, and cybercrime, said Dr Sanaullah abbasi, PhD in law and former director general of the Federal Investigation Agency.
Dr Abbasi examines the intersection of crime and anonymity on the dark web, integrating theoretical perspectives like Routine Activity Theory and Strain Theory. Additionally, a Pakistani perspective highlights the nation’s growing challenges with dark web-facilitated cybercrimes.
He elaborated that the internet comprises three layers; the surface web, the deep web, and the dark web, while the deep web includes non-indexed content like academic databases and private information, the dark web is a subset that requires specific encryption software, such as Tor or I2P , to access.
Due to its architecture, the dark web allows users to operate anonymously, making it attractive to individuals and groups engaged in illegal activities (Gehl, 2018). According to his investigations, the dark web enables criminal activities, applies criminological theories to explain its dynamics, and examines its implications for Pakistan.
Crime & anonymity
Dr Sanaullah Abbasi said the dark web fosters various criminal activities, including drug trafficking, and dark web marketplaces, such as Silk Road and AlphaBay, have revolutionized drug trade by offering anonymity to both buyers and sellers. These platforms operate with cryptocurrencies, complicating efforts to track financial transactions.
Human traffickers exploit the dark web to advertise illegal services and exploit victims while evading law enforcement. Child exploitation materials are also traded extensively on these platforms, posing significant ethical and legal challenges.
Data theft
The dark web is a hub for selling stolen data, including credit card details, personal information, and hacking tools. “Ransomware as a Service” (RaaS) kits, available on the dark web, enable even novice criminals to launch sophisticated cyberattacks.
Dr Abbasi said illegal arms sales and terrorist communications have flourished on the dark web. Groups like ISIS have reportedly used the platform for propaganda, recruitment, and financial transactions
He said that In Pakistan, the dark web poses unique challenges due to a combination of technological and socio-economic factors by private and public enterprises. Cybercrime trends statistics have identified an increase in cybercrimes originating in Pakistan committed on by both sides of social contract including credit card fraud, identity theft, and hacking. Many of these activities involve transactions on the dark web.
Illegal marketplaces
Dark web platforms facilitate the trade of drugs, counterfeit passports, and even weapons, some of which are linked to criminal organizations operating in Pakistan.
The former FIA DG said Pakistan’s cybercrime laws, such as the Prevention of Electronic Crimes Act (Peca), are limited to addressing crimes facilitated by the dark web. The lack of technical expertise and infrastructure hampers law enforcement’s ability to monitor and prosecute offenders.
Ethical implications
The anonymity provided by the dark web raises ethical concerns; privacy vs. security, while encryption protects whistleblowers and dissidents, it also shields criminals. Successful operations like the takedown of AlphaBay and Hansa Market illustrate the importance of international collaboration in dismantling dark web criminal networks. Advances in artificial intelligence and blockchain monitoring offer potential solutions for regulating dark web activities without infringing on individual privacy.
Solutions
Dr Sanaullah Abbasi said the dark web represents a double-edged sword. While it ensures privacy for legitimate users, its anonymity is a significant enabler of crime. Routine Activity Theory and Strain Theory offer valuable insights into why criminal activities proliferate in such environments. From a Pakistani perspective, addressing dark web crime requires enhanced cybersecurity infrastructure, better enforcement of existing laws across board on both sides of social contract as privately and state sponsored criminality included and international cooperation. Balancing privacy rights with effective regulation will be crucial to mitigating the dark web’s risks while preserving its legitimate uses.
Solution; Abbasi said that, these are crimes like Illicit Marketplace, the most famous type like a black-market Amazon for; Drugs (both illegal and prescription), firearms and weapons, Stolen data (credit cards, login credentials), hacking tools and services and Counterfeit money and documents.
He added that, the Cybercrime Services, Hiring hackers for DDoS attacks, creating malware, or breaking into systems. For Financial crimes, Cryptocurrency scams, money laundering, and fraud and for extremist and Terrorist activity a communication, recruitment, and funding, while the for the disturbing and Illegal content, this includes some of the most heinous material, such as child exploitation content.
Dr Abbasi suggesting solutions to these crime said that, solving crimes on the Dark Web is a complex cat-and-mouse game that blends traditional police work with advanced digital forensics. This is the most common and effective method. Law enforcement officers create fake profiles and infiltrate criminal forums and marketplaces. They pose as buyers or sellers to gather evidence and identify key players. They gain the trust of criminals over weeks or months to uncover their real identities and operations.
Blockchain Analysis; while Bitcoin and other cryptocurrencies are pseudo-anonymous, they are not untraceable. Every transaction is recorded on a public ledger (the blockchain). Specialized firms (like Chainalysis and CipherTrace) analyze the blockchain. When a criminal converts cryptocurrency to real money on a regulated exchange, their identity is often revealed, allowing investigators to trace the funds back to the illicit activity.
-
 King Charles, Camilla To Snub Prince Harry’s America Meet-up Attempt
King Charles, Camilla To Snub Prince Harry’s America Meet-up Attempt -
 Zendaya Crashes Young Couple Wedding In Las Vegas
Zendaya Crashes Young Couple Wedding In Las Vegas -
 Patrick J. Adams Breaks Silence On How 'The Madison' Role Echoed Family Loss
Patrick J. Adams Breaks Silence On How 'The Madison' Role Echoed Family Loss -
 Prince William, Kate Middleton Push Drastic Changes
Prince William, Kate Middleton Push Drastic Changes -
 Prince William Has ‘little Forgiveness’ In Heart For Prince Harry
Prince William Has ‘little Forgiveness’ In Heart For Prince Harry -
 Netflix Eyes Shock Revival Of 'The Crown' After Andrew Mountbatten Windsor Controversy
Netflix Eyes Shock Revival Of 'The Crown' After Andrew Mountbatten Windsor Controversy -
 Jennifer Aniston's Beau Jim Curtis Becomes Her Guiding Light
Jennifer Aniston's Beau Jim Curtis Becomes Her Guiding Light -
 Prince Harry, Meghan Markle Swimming Dangerous Waters With Australia Trip
Prince Harry, Meghan Markle Swimming Dangerous Waters With Australia Trip -
 Lewis Hamilton Warned Against Kim Kardashian Romance To Save Brand Name
Lewis Hamilton Warned Against Kim Kardashian Romance To Save Brand Name -
 'American Pie' Star Shannon Elizabeth Makes Rare Admission About Legacy Role
'American Pie' Star Shannon Elizabeth Makes Rare Admission About Legacy Role -
 Prince William Spectates Team Wales During Rugby Match In Cardiff
Prince William Spectates Team Wales During Rugby Match In Cardiff -
 Teyana Taylor Drops Cryptic Hint About What Could Happen At The Oscars
Teyana Taylor Drops Cryptic Hint About What Could Happen At The Oscars -
 Andrew Mountbatten Windsor, Sarah Ferguson 'flagged By Intelligence Services'
Andrew Mountbatten Windsor, Sarah Ferguson 'flagged By Intelligence Services' -
 Kim Kardashian Headed For Another Love Crash With Lewis Hamilton
Kim Kardashian Headed For Another Love Crash With Lewis Hamilton -
 Kris Jenner Recalls Trying To Save Kylie Jenner From 'biggest Failure' Of Life
Kris Jenner Recalls Trying To Save Kylie Jenner From 'biggest Failure' Of Life -
 Britney Spears Leaning On The Kardashians Post DUI Arrest
Britney Spears Leaning On The Kardashians Post DUI Arrest